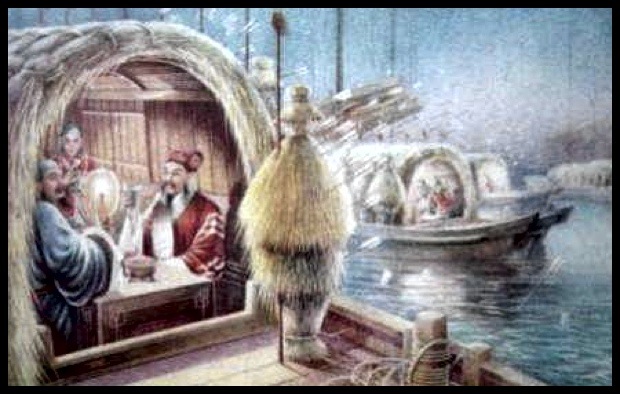
草船借箭:Artist rendition of Chinese strategist Zhuge Liang collecting enemy arrows with a fleet of straw boats.
There is a group of U.S. analysts who seem fascinated by the supposed influence of ancient Chinese military thought on contemporary Chinese security policy. In The China Threat, Bill Gertz suggests the stratagems articulated in Sun Zi’s Art of War guide a concerted Chinese effort to use unwitting “pro-Beijing” U.S. China analysts to manipulate U.S. policy.
The imagined Chinese plan is to subdue the United States without firing a shot using espionage and propaganda. Gertz’s “blue team” of U.S. China analysts claim they see through the subterfuge. Their goal is to make U.S. policy-makers aware that China is concealing its military preparations and disguising its aggressive intentions behind the reassuring voices of an influential “red team” of U.S. experts who are either coerced or duped into downplaying the China threat.
Gertz apparently does not consider the possibility that unsuspecting “anti-Beijing” analysts on the blue team could also be manipulated into serving Chinese ends.
Not Sun Zi, but Zhuge Liang?
During the Three Kingdoms period (A.D. 220-280), Zhuge Liang, a legendary Chinese strategist, employed a clever tactic immortalized in the Chinese idiom “using straw boats to catch arrows” (草船借箭). The historical event on which it is based is not widely understood, but the meaning of the idiom, as it has been passed down through the ages, is simply to use one’s wits to employ the resources of an opponent for one’s own ends. As the tale is told Zhuge Liang sent a fleet of straw-covered boats (see the illustration above) against an opponent, which attacked the faux armada with its archers. In addition to exposing the opponent’s position, the straw boats caught the arrows, which Zhuge Liang collected and turned over to a doubtful patron he promised to arm with 10,000 new arrows in just three days.
Is it possible that rather than hiding their strengths, Chinese military propagandists are exaggerating them and using U.S. analysts to help them do it? Could the blue team unknowingly be aiding and abeting Chinese psychological warfare by making the Chinese military appear stronger and more capable than it actually is?
Confusing Chinese Sources
Over the past several decades, Gertz and the blue team have penned hundreds of articles exposing supposedly secret information on new Chinese weapons that exploit imagined U.S. vulnerabilities. Blue team analysts call them “assassins mace” weapons, parroting, in translation, a term used by Chinese military propagandists to describe hypothetical technological “trump cards” China could play in a contest with the United States. The evidence for the existence of many of these “assassin’s mace” weapons is highly questionable. Sources described as Chinese government reports or statements of official Chinese military policy routinely turn out to be magazine or newspaper articles written by Chinese propagandists.
The latest blue team false flag of a Chinese source appeared on 30 July 2013 in the Washington Free Beacon. What Gertz identified as “an internal Chinese defense report” on Chinese plans for a “people’s war in cyberspace” is actually an openly published four-page article by four engineers from the Shanghai Satellite Engineering Institute, a subsidiary of the China Aerospace Science and Industry Corporation (CASIC) best known for its contribution to the development of China’s weather satellites.
The downloadable article is available through China’s CNKI database. Gertz describes the so-called “internal report” as “a rare inside look of one of Beijing’s most secret military programs.” It isn’t. Hundreds of similar Chinese articles are published every year. Chinese defense analysts sometimes refer to them as “garbage articles” that are more often then not intended to pad the author’s publication list. They are often written by people who have an interest in the topic but no inside knowledge about actual military programs.
In this case the authors provide an interesting academic discussion of the military connections between space and cyber similar to those I heard in person at a recent conference at China’s National University of Defense Technology in Changsha. Like many of these articles, most of the concepts it discusses are taken from U.S. sources. The authors’ purpose is to introduce and explain these concepts to a Chinese audience, not to describe Chinese ideas and plans. The U.S. government translated the article and marked the translation “For Official Use Only,” even though the article itself is openly available over the internet. The restrictive categorization may be why Gertz thought the article was more secretive, important, and rare than it actually is.
The Danger of Exaggeration
Although U.S. analysts who dig through Chinese texts for alarming statements may believe they are performing a public service, there is a danger in misrepresenting what they find. U.S. freedom of action in the area surrounding China is constrained as much by U.S. perceptions of Chinese capabilities as it is by the capabilities themselves. Overestimating those capabilities unnecessarily restricts U.S. decision-makers who may feel the need to respond to disagreeable or threatening Chinese behavior.
It is in China’s interest to have U.S. decision-makers believe China’s military is stronger than it actually is. Moreover, most of the sensational claims about Chinese capabilities published in the U.S. by the blue team are repeated by the Chinese press, providing the added benefit of making the Chinese military look more impressive to the Chinese public as well. Perhaps this is why Chinese military propagandists publish so many articles about supposedly secret Chinese “assassins mace” weapons.
The next time the blue team decides to write a missive on the China threat they may want to set aside Sun Zi’s Art of War and pick up the tale of the straw boats of Zhuge Liang.
